Just kicking trying to manage my CopyFail nausea.
Post
Long fingers today, in many machines. Dozens of services patched, host machines alongside.
I've typed `uname -a` a great many times in my life, but I don't think as many in one day.
Debian's patched 6.12.85+deb13-amd64 #1 SMP PREEMPT_DYNAMIC seems GTG with the PoC published here:
https://github.com/theori-io/copy-fail-CVE-2026-31431/blob/main/copy_fail_exp.py
```
root@cake:~# su - eat
eat@cake:~$ vim foo.py
eat@cake:~$ cat foo.py | python3 && su
Password: su: Authentication failure
Password:
```
Bit worried about where Ubuntu is at. Ominously, their own fix announcement page seems down:
https://ubuntu.com/blog/copy-fail-vulnerability-fixes-available
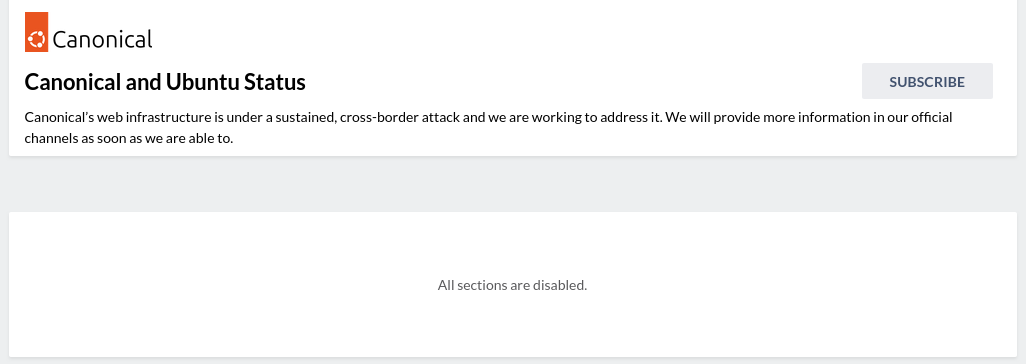
@ctoney sent through this helpful update. It appears Ubuntu web infra might be under DDoS rn https://status.canonical.com/
A bit odd. Ubuntu's status page currently looks like this.
If this is a DDoS, it is a very expensive one. Someone with a lot of money and spite.
I went through a bunch of VMs post patch and found one that had algif_aead loaded & so the PoC passed.
If that module is loaded, you're still vulnerable.
EDIT, for Debian family:
Blacklist like so:
```
modprobe -r algif_aead
```
Then put this into a /etc/modprobe.d/blacklist-aead.conf:
```
blacklist algif_aead
install algif_aead /bin/false
```
Then:
```
/sbin/update-initramfs -u -k all && reboot -n
```
@JulianOliver dedication to the nth degree
@kategenevieve Phew, doing my best at least. I had other plans for today argh!
@JulianOliver ha ha ha the computers don't care about your human plans. they need *all* your time.
You could disallow the specific crypto module, if it is compiled as a module rather than into the main
... but don't extend your class to include "here's how to recompile your kernel"!!!
@futuresprog Hehe, I would have to add a day for that!
This distros I work with have been very quick to patch, and so I currently have fingers in many servers, and their many guests, getting them sorted. TBH I had different plans for today, but such is #sysadminlife
@JulianOliver Have you considered doing a Fortress session with OpenBSD or FreeBSD?
@pertho FreeBSD I have yes. The tricky bits come down to ease of use on the hypervisor. More so most or all of the guests themselves would need to be GNU/Linux due to going with official deploys for the services they host. I would also need to do the pre-training (Tunnel) on a *BSD also, to get people in the zone.
One for the future. Would be great. Just raises the entry barrier a little, maybe making for longer sessions.
@JulianOliver @pertho This would be neat - I keep a FreeBSD host at home and I get the occasional temptation to rebuild with jails and full ZFS. Still <3 debian though.