Listening to cybersecurity people freak out over Mythos is so tiring. Like, bro, your local water treatment plant runs Windows XP, your mobile provider's hardware is older than you are, and the protocol that routes internet traffic is secured by everyone just agreeing that hijacking it would be uncool.
Post
@malwaretech don’t ask how old the code your bank runs on is.
@malwaretech when I worked at Sprint, we had to figure out crazy workarounds because if we update IE from a version that was 5 years old at the time, none of the system portals would work
@malwaretech and everyone is still getting phished!
@malwaretech I bet there are still some people still running control systems on NT 4.0. Nice and "secure" because it doesn't support USB. Win95 probably lurking in the controller off many CNC machines too.
@malwaretech The 'cybersecurity' people I hear speaking of gloom and doom also happen to have a product ready to release in a week or two, but can't demo it or explain what it actually does. They're selling.
@malwaretech yet another thing that needs my ministry I suppose; something something implementation diversity
@malwaretech Is Mythos any good though? I can't find any actual results through all the hype.
@malwaretech ah just like SS7, vulnerable since 1975, still in use, still vulnerable 😂
@malwaretech hey man, it would be really cringe if you misused the protocols that allow us to route internet traffic. Seriously, it would be great if one of these companies would come out with a comic book villain product that was meant to help users and corps efficiently remediate their vulnerabilities instead of exploiting them. Not to mention the hype. Mythos seems to only mark a tangible improvement over previous models in its testing, not the end of security as we know it. The initial article about Mythos sounds like one of the marketing team just played *Hacknet* and really likes the idea of the super hacker tool that can hack all the things when you type "./hack" into a terminal.
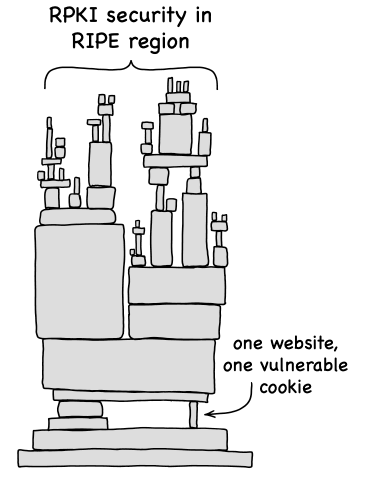
@malwaretech be fair! We secured BGP with lots of crypto, but then left an XSS exploit in the crypto control panel allowing your entire network to get de-routed with one mis-click. https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
Fuck Mythos and marketing bullshit, but AI that immensely reduces time-to-exploit is real. Companies are not prepared for it.
@malwaretech The Internet being held together by string and bubble gum is not far from the truth.
@malwaretech I think you're right about the hype level but I think there is something to the idea that all of the places which were gambling on obscurity as their primary defense are probably going to find that strategy looks even worse.
@malwaretech excellent point.
A lot of infrastructure runs outdated software.
But thankfully, most of these systems are not connected to the internet.
@malwaretech And your company CEO's password is password.
Well only hijack / hack mobile connection when it's really necessary like when your princess has escaped and you want to kidnap her back.
@malwaretech I think it would be kinda cool.
@malwaretech I work in a large company that was hacked last year. Many modern systems were compromised. The RS6000 box and several of our ancient mainframes were untouched and weren't even turned off during the lockdown or recovery. Gave them a quick once over and they kept ticking like it was 1999.
"Using encryption on the Internet is the equivalent of arranging an armored car to deliver credit card information from someone living in a cardboard box to someone living on a park bench"
(Gene Spafford)
@malwaretech I think you underestimate how ancient some of us are. I'm definitely older than anything my mobile provider owns, cos I'm older than the industry.
@malwaretech I truly don't understand it. CISOs and managers are jizzing themselves from snake oil is not new but form technical people I'd expect more.
@malwaretech now now, don't be raggin' on my local water treatment plant, they're much more up to date than that. they run Windows Vista.
@malwaretech (don't ask about the Windows NT4 machine in the PLC cabinet. nobody knows what it does but we're all too scared to turn it off in case the 5GB Maxtor hard drive in there dies during spinup)
@gsuberland @malwaretech it's scary 'cause it's true 🫣
@floe @malwaretech it's based on real events :D
@malwaretech I liked the days when we were panicking about China listening in on all our telephone calls / scooping up our mobile data.
Now we just talk directly to some American company's AI and ask them to diagnose our medical problems that we're too embarrassed to see a real doctor for.
@malwaretech 😉 (although bgp isn't as bad as it was in practice the days, but point made!)
@malwaretech Not to mention that this isn't new...LLMs have been able to do this since day one. And small models found the same vulnerabilities in FreeBSD ¯\_(ツ)_/¯
Also, from what I understand Mythos couldn't actually make an exploit for that bug, sooooooo big marketing stink imho.
@malwaretech I don’t care, if this puts security back on the agenda, I’ll take it…