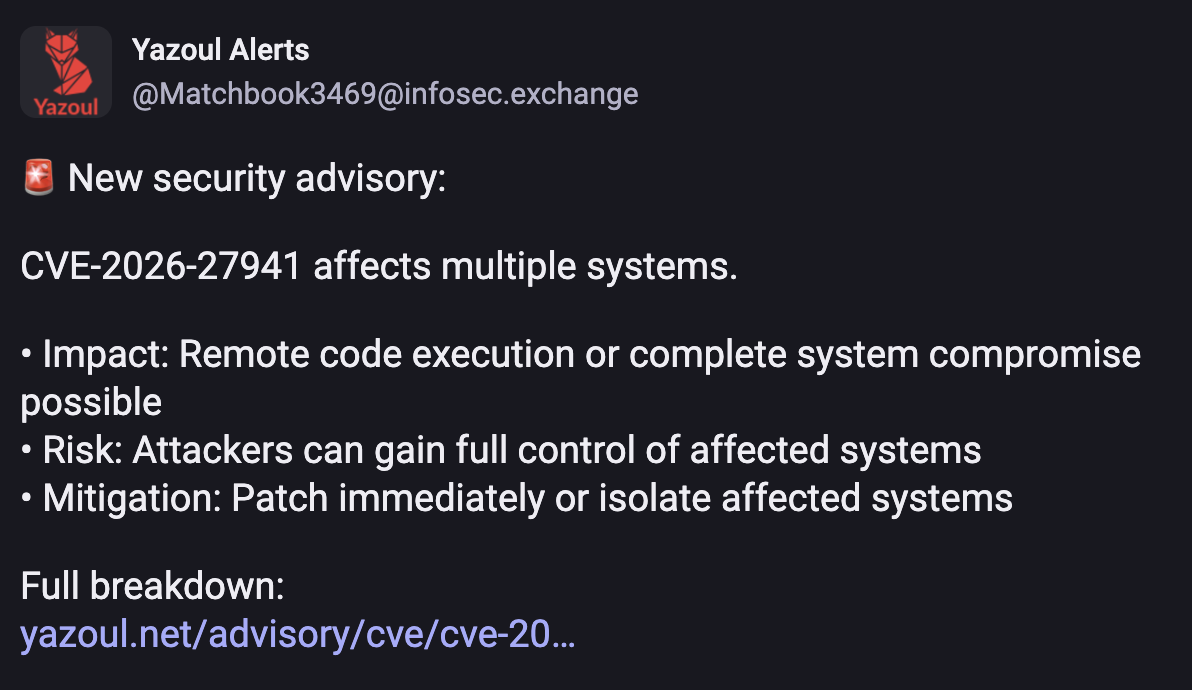
Hey, security vendors.. this is a bullshit anti-pattern. This vendor and others like it intentionally leave out the impacted vendor, products, technologies, and environments. There is zero context here. Readers would need to follow the link or independently research the CVE to see if they care.
Security practitioners see it for what it is: Fear based traffic farming.
It isn't a good look and many of us will never trust anything you say or send you traffic.
A note, I do work for a security vendor. We don't do this and I would absolutely call out our (awesome) marketing or research teams if we did.