The scale of meshtastics avoidance of building security into the design is pretty epic.
It allows for the formation of an entire mesh just for MITMing it.
This ONE liner here in the PKI attack means that once a node gets poisoned the key we created is based on the MAC so -anyone- who knows your MAC can read your MITM'd traffic.
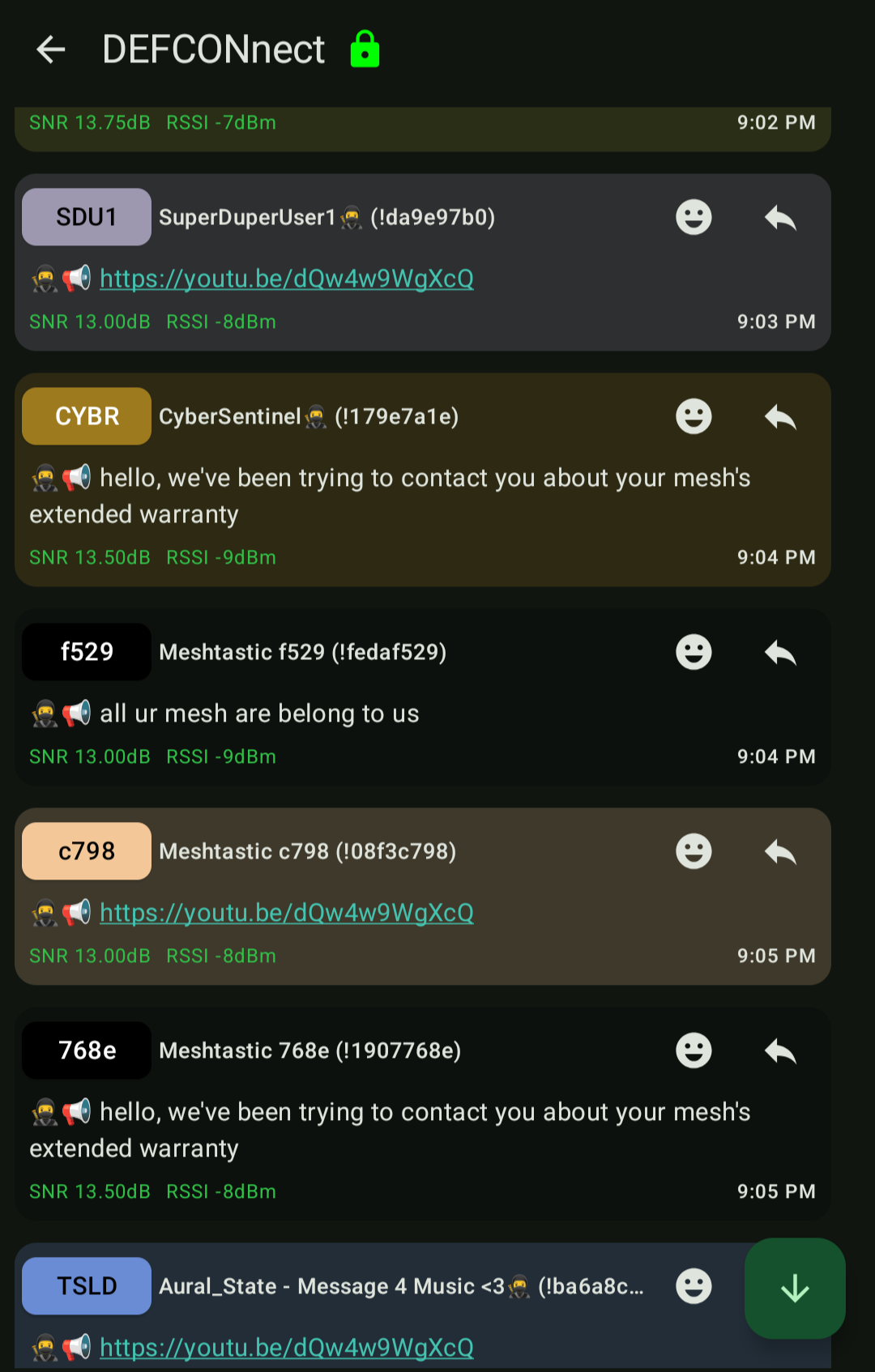
When attackers run mesh marauder against the DEFCON 33 firmware they are all working together. Anyone in range can read the MITM'd DMs.
https://github.com/datapartyjs/meshmarauder/blob/channel-chat/src/lorapipe-raw-packet.mjs#L191-L193